Identified as HotNews SAP Note #2934135 (CVE-2020-6287) in the July 2020 SAP Security Notes mentioned in our earlier blog SAP Security Patch Day, the RECON (Remotely Exploitable Code On NetWeaver) vulnerability has a CVSS score of 10 out of 10 (the most severe) and can potentially be exploited, impacting the confidentiality, integrity and availability of mission-critical SAP applications.
A successful exploit of RECON could give an unauthenticated attacker full access to the affected SAP system. This includes the ability to modify financial records, steal personally identifiable information (PII) from employees, customers and suppliers, corrupt data, delete or modify logs and traces, and other actions that put essential business operations, cybersecurity and regulatory compliance at risk.
1. Test the Vulnerability
2. Recommendation
Test the Vulnerability
Let’s use an unauthenticated method simulating an attacker who goes on to create SAP JAVA users, including one with Administrative privileges to gain access to the SAP JAVA application. Notice no password was needed after the attacker compromised the network access to the SAP environment.
Create SAP JAVA user:
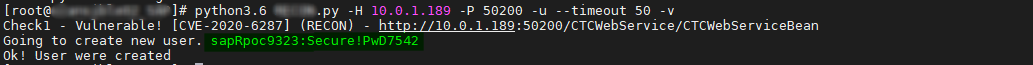 Figure 1: Create SAP Java User
Figure 1: Create SAP Java User
Figure 2: Identity Management Overview
Create SAP JAVA Administrator user:
Figure 3: Create SAP Java User
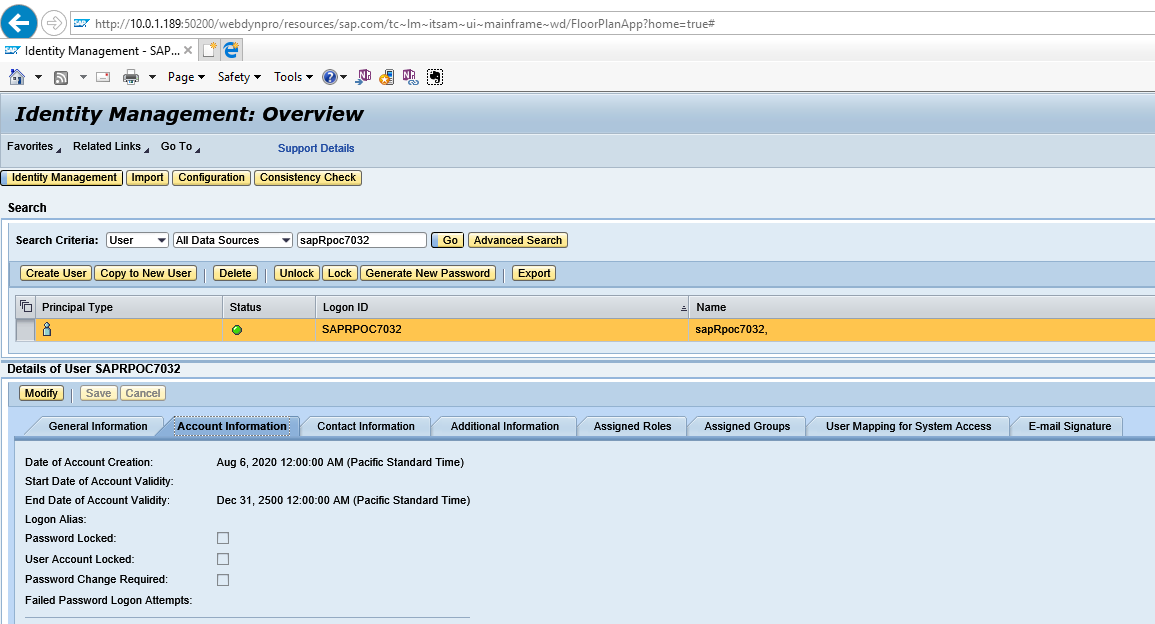 Figure 4: SAP Java Overview 1
Figure 4: SAP Java Overview 1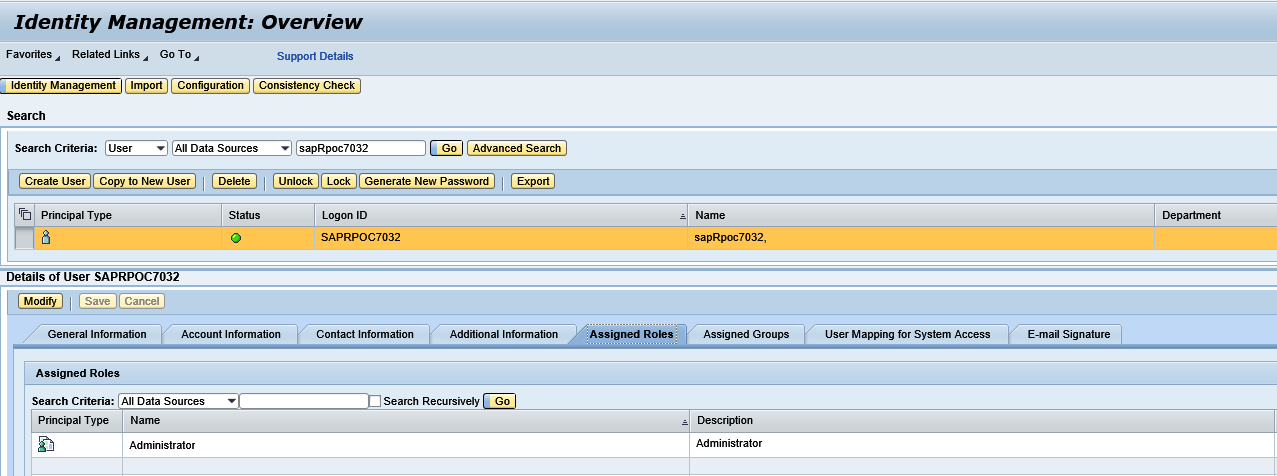
Figure 5: SAP Java Overview 2
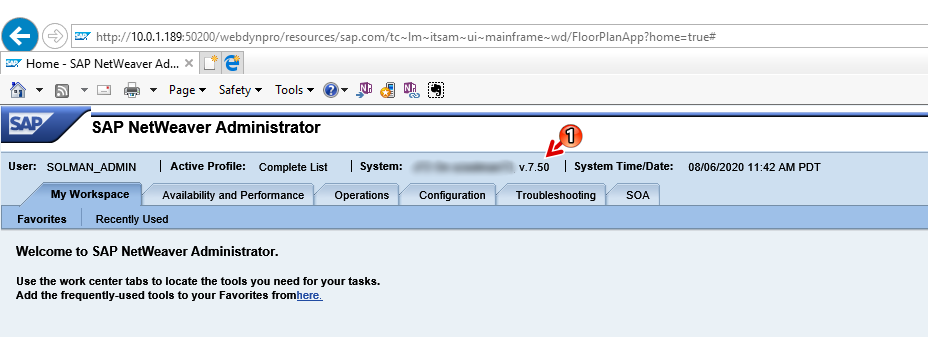
Figure 6: SAP Java Netweaver Administrator
Recommendation
Current SAP customers should refer to SAP note 2934135 - [CVE-2020-6287] Multiple Vulnerabilities in SAP NetWeaver AS JAVA (LM Configuration Wizard) and 2939665 - Disable/Enable LM Configuration Wizard | Critical API's in LM Configuration Wizard for patch information.
There are hundreds of services delivered with SAP JAVA application, and even more when you run business applications such as PI/PO. Stay vigilant in monitoring and managing the security aspects of your applications particularly with security vulnerabilities and patching.
Find these blog articles useful? Subscribe to our blog if you haven't already done so, or give IT-Conductor a test drive to see how we can help monitor and manage your SAP landscape remotely, without the typical security issues of installing and managing your own technical monitoring infrastructures.
